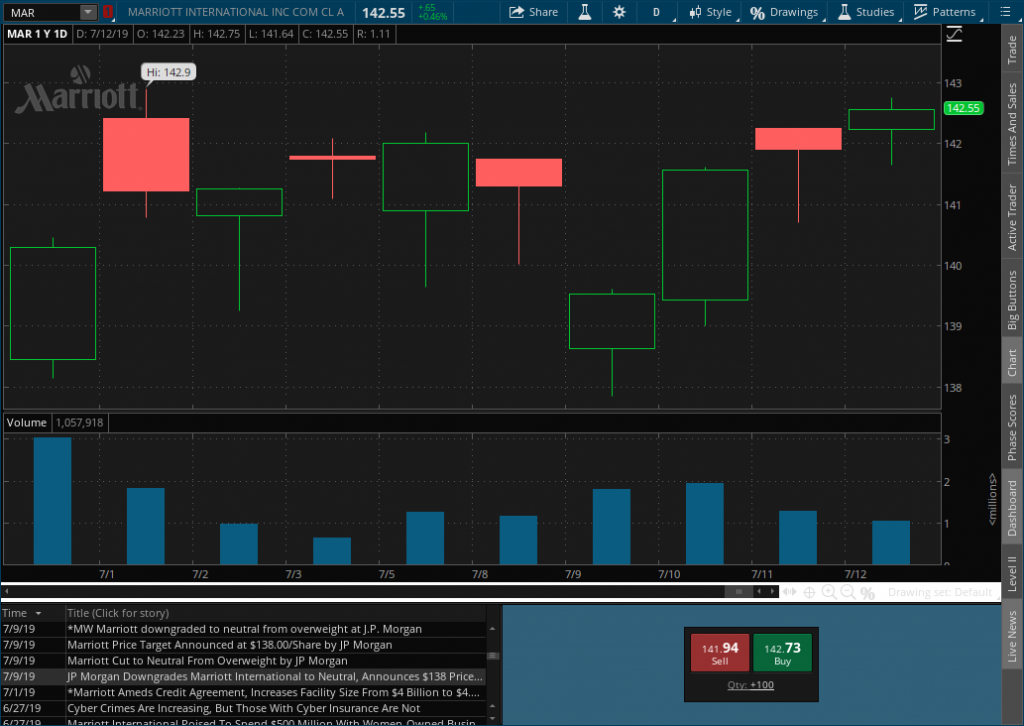
We haven’t had a good hack in some time and our market theories are continuing to ring true. First lets look at charts.
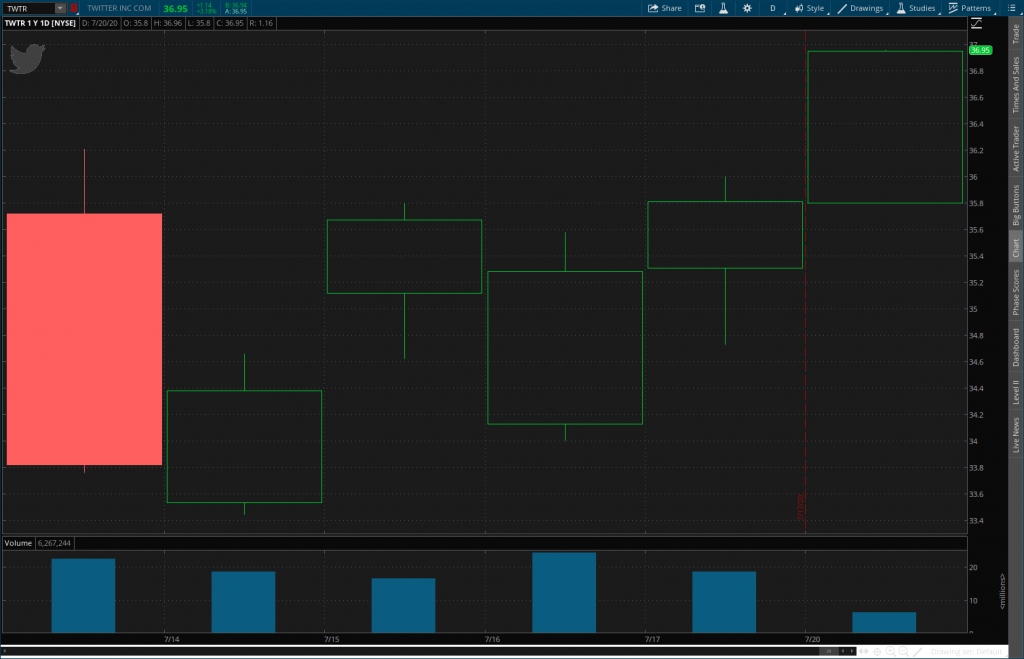
The day of the 15th TWTR dropped “heavily” after hours as reported by The Verge. Call it roughly 6% after hours while the NASDAQ ETF QQQ was also down 3% after hours. Is this unusual movement?


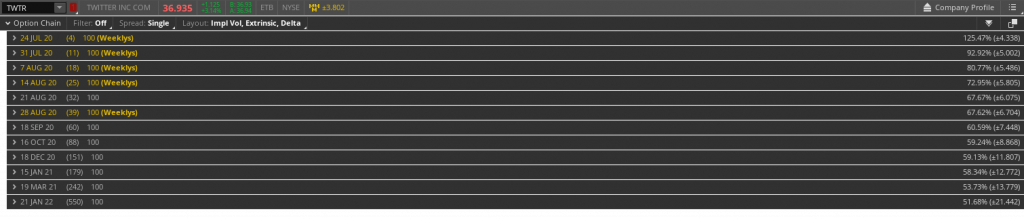
This move is within expectations. If we look at the expected move (1 standard deviation) on a one week period is +/-4.338. TWTR closed at 35.67 the day the hack hit the press. TWTR opened at 34.16 the next day well within the expected move.
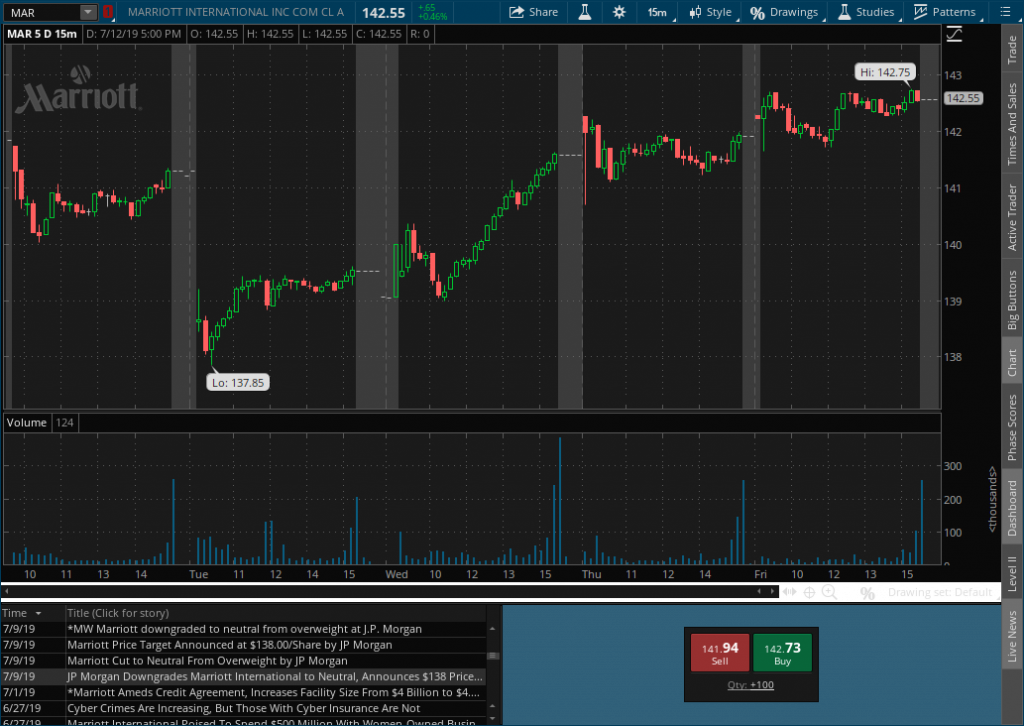
If you look at the after hours charts above it might be scary if you don’t understand the market. If we roll out to a daily chart you can see that TWTR has been green since the 15th and recovered to above its high on the 15th by the 17th. Today TWTR has cleared $37.00, above its 6/8 high of $36.94.
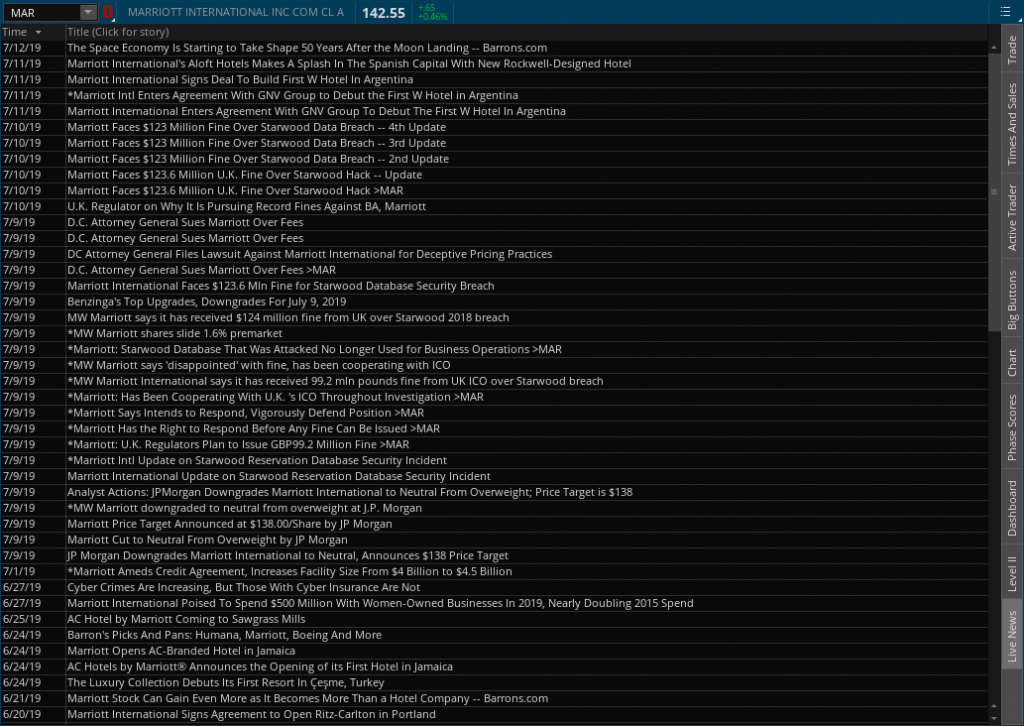
Let’s also look at analysts calls. On 7/20 Goldman Sachs raises price target to $43 from $39. This is the Monday after the hack hit the press. On 7/15 JPMorgan raises to $33 from $29. On 7/9 Morgan Stanley raised to $32 from $24 What do we see here? A trend that the people who are paid follow the stock believe its going higher regardless of the news.
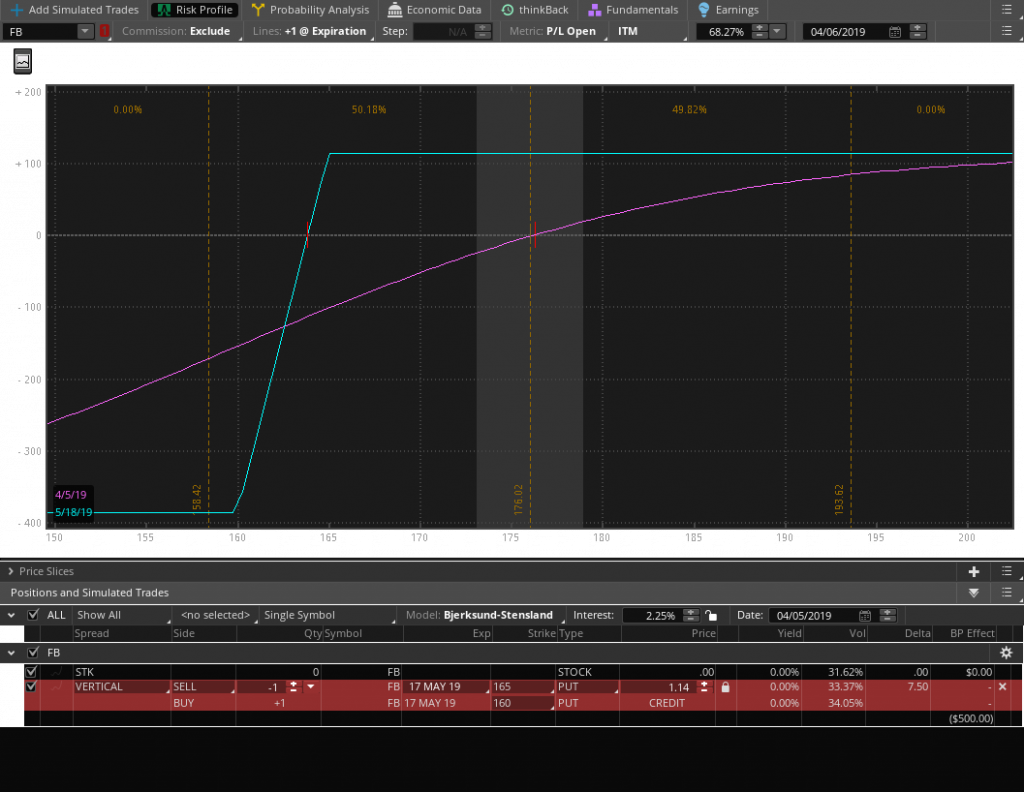
This continues to support our thesis that hacks do not materially affect large companies. The upstream aspects of customer satisfaction, reputational loss, etc. are not predicted to affect the balance sheet, income statement, and cashflow statement, thus fundamental investor sentiment is unchanged as a result of the news. Technical investors are always looking for a dip to buy which bad news always presents an opportunity to buy stock, buy a limited risk call strategy, or sell a limited risk short put vertical.